Diploma fraud is not just a fake degree printed in someone’s basement.
More often, it shows up in ways that are harder to catch at a glance: altered transcripts and credentials from diploma mills dressed up to look legitimate.
That is the real problem. Not just that fraud exists, but that it often gets mixed into systems built for speed, volume, and trust.
When that happens, everyone pays for it.
Universities lose control over the value of the credentials they issue. Employers waste time validating claims that should be easy to confirm.
Graduates who earned their degrees honestly end up in a market where legitimate credentials are questioned more often because fake ones keep circulating. The Council for Higher Education Accreditation has tracked how degree mills operate for years and why they continue to find buyers and loopholes.
None of this is new. But it has become easier to scale. Cases like the Axact scandal made that obvious. Fake credentials were being produced and sold globally, at volume, through an operation that looked far more sophisticated than most people expect when they hear the phrase “diploma fraud.”
Add better design tools, better printers, easier online distribution, and the gap between a real document and a fake-looking-real one gets smaller fast.
Let’s look at how we can get ahead of this problem.
Current Challenges in Diploma Verification
Here’s what’s holding us back when it comes to verification.
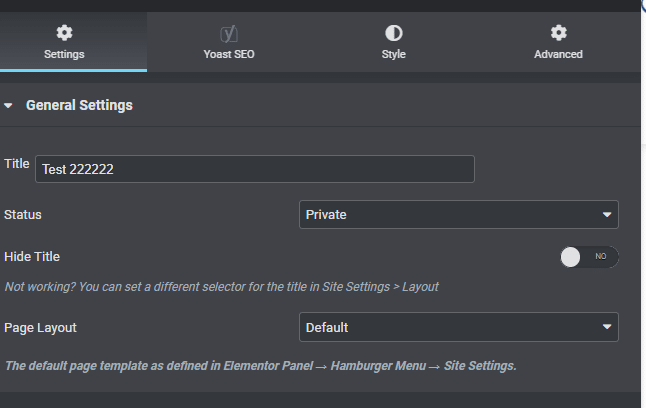
Traditional verification processes
A lot of diploma verification still runs on manual effort.
A phone call to the registrar. A confirmation letter. A sealed transcript. An email thread between an employer, a graduate, and a records office already buried in requests.
These methods can work, but they do not work well at scale, and they do not leave much room for speed when teams are short-staffed, or requests spike around graduation, hiring season, or cross-border admissions cycles.
This is where the process usually starts to break.
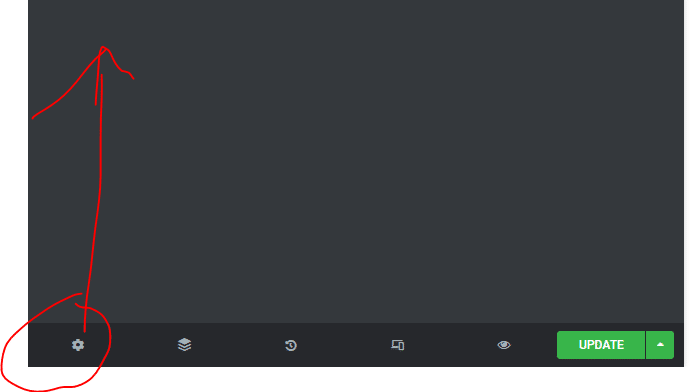
A document leaves the institution, gets forwarded three times, downloaded twice, renamed, rescanned, and eventually reviewed by someone who has no direct way to tell whether what they are looking at is original, altered, or partially fabricated. This was an issue, even in 2004, as you can see below.
Even when no fraud is involved, the process is slow. When fraud is involved, slowness helps it.
Jeff Zhou, CEO and Founder of Fig Loans, leads a financial platform that regularly evaluates applicant documentation and identity records as part of lending decisions, which makes verification reliability a constant operational concern.
He explains, “Manual verification processes create too many points where information can lose its chain of trust. Once a document has been downloaded, forwarded, renamed, or rescanned a few times, the question is no longer just whether the credential is real. It becomes whether anyone can confidently prove it is unchanged.”
SHRM has reported similar concerns, which helps explain why employers increasingly want faster and more reliable ways to verify credentials before they make hiring decisions.
Verification should not depend on how persistent the person on the other end is willing to be.
Technological and logistical obstacles
Universities do not stay on older systems because modernization is hard in exactly the ways higher-ed projects tend to be hard.
Privacy rules matter. FERPA limits how student records can be handled.

GDPR adds another layer in Europe and in any system touching data across borders.
Legacy student information systems are often deeply embedded and not easy to replace or even integrate cleanly. And a project that sounds straightforward on paper can stall quickly once it has to move through procurement, compliance review, governance, and interdepartmental approval.
So institutions end up in a familiar place: they know the old process is inefficient, but the path out feels bigger than the immediate problem they are trying to solve.
That is how pilot projects get stuck.
Kashif Ali, Growth Specialist at PsychologySchoolGuide.net, works closely with universities and academic institutions that help prospective students navigate legitimate degree pathways.
He notes, “Many universities are already thinking carefully about how to modernize credential verification. The challenge is coordinating technology, compliance, and internal systems at the same time. But when institutions take that step, the long-term payoff is a much more transparent and trustworthy academic ecosystem.”
The Solution: Secure Verification Systems
The biggest shift in secure verification is simple: authenticity travels with the credential.
That changes the whole process.
Instead of asking employers or licensing bodies to trust a PDF because it looks official, secure verification systems attach proof that the credential was actually issued by the institution and has not been changed since.
Now, that can take different forms.
- Digitally signed diplomas.
- Tamper-evident PDFs with unique identifiers.
- Online verification portals.
- Verifiable credentials that can be checked across systems.
- Blockchain-anchored records on a distributed ledger.
The format matters less than the function.
Bryan Henry, President of PeterMD, works in a healthcare environment where confirming professional qualifications and training credentials is a fundamental part of maintaining patient trust.
He explains, “Secure verification systems strengthen the credibility of the credential itself. When authenticity travels with the document through digital signatures or verifiable records, it gives institutions, employers, and graduates confidence that the achievement being presented is both genuine and properly documented.”
What matters is that the institution is no longer relying on appearance, manual confirmation, or repeated staff intervention as the main line of defense.
W3C’s Verifiable Credentials standard is important here because it defines a way to issue and verify claims across platforms while limiting unnecessary data exposure.
Blockchain, for example, creates an immutable record that eliminates the possibility of tampering.
When universities issue credentials on a distributed ledger, employers can verify authenticity instantly. This reduces a weeks-long process into a matter of seconds.
Case Studies of Successful Implementation
There are already working models we can look at.
MIT used the open Blockcerts standard to issue blockchain-anchored diplomas, giving graduates a credential they can share and others can verify without routing everything back through the registrar.
It removed one of the biggest weak points in older systems: constant dependence on manual confirmation.
The European Union’s European Digital Credentials for Learning initiative tackles a different version of the same problem. Recognition across borders is messy even when credentials are legitimate. Standardized, digitally signed credentials make that process more reliable.
In the U.S., the National Student Clearinghouse has shown the operational side of this at scale. Centralized degree verification reduces phone calls, reduces manual follow-up, and takes routine verification work off already stretched registrar teams.
The common thread is that these systems reduce ambiguity.
Ryan Walton, Program Ambassador for The Anonymous Project, works with organizations that preserve historical materials where provenance and authenticity are essential.
He says, “One of the most encouraging shifts we’re seeing is the move toward systems that make verification easier instead of harder. When institutions adopt tools that clearly confirm authenticity, it helps everyone involved trust the record with far less uncertainty.”
So there are fewer opportunities for someone to slip a fake into a process built on trust and delay.
Digital Credential Tracking as a Solution
A physical diploma can prove that someone has a document. It does not prove that the version in circulation is unchanged, current, or authentic unless someone manually checks it. A digital credential system closes that gap.
Compared with a physical diploma, digital credentials can:
- Prove authenticity in seconds
- Limit data exposure to only what needs to be shared
- Move across borders without relying on notarization or manual translation workflows
- Connect more easily with job platforms and licensing boards
Sixin Zhou, Marketing Manager at LDShop, works with digital platforms where secure identity verification and reliable records are essential to maintaining trust across global users.
He notes, “Digital credential tracking brings a level of clarity that traditional documents simply can’t offer. When institutions maintain verifiable records that can be checked instantly, it gives graduates a more portable and trusted way to share their achievements.”
How to Implement Digital Credential Systems
The mistake here is trying to digitize everything at once.
- The institutions that handle this well usually start smaller and make deliberate choices early, because those choices shape everything that comes after.
- Define scope. Not every credential has to move first. Choose an area where the operational pain is already obvious, and success can be measured clearly.
- Choose standards carefully. If a university adopts a system that cannot interoperate cleanly, it may solve a short-term problem and create a longer-term one.
- Privacy and compliance need to be designed into the process from the start, not reviewed after the system is chosen. That means aligning with FERPA, GDPR, and internal data policies, while limiting what a verifier can see to what is actually necessary.
- Universities need partners who understand student records, accreditation, issuance workflows, and the timing realities of higher ed. A provider that is good at generic document security is not automatically good at registrar operations.
- Training matters too. A credential system can be technically sound and still fail if registrars, IT teams, career services staff, and graduates do not know how to use it confidently.
Start with one school, one credential type, or one program. Gather feedback from graduates, employers, and staff.
And then fix what confuses. Then expand.
Best Practices for Universities and Higher Education Institutions
If credential issuance, revocation, correction, and access are not governed clearly, a university can end up with a secure-looking system layered on top of inconsistent internal practices.
- Policy has to define who can issue credentials, who can change them, who can revoke them, and what identity checks are required before anything is released.
- Name changes, record corrections, duplicate credentials, retention periods, and access permissions all need to be addressed directly. These are not side issues. They are the situations where confusion usually appears first.
- And policy cannot be written by one office in isolation. Registrars, IT, legal, academic affairs, and alumni-facing teams all touch different parts of the credential lifecycle. If they are not aligned, the system will reflect that misalignment.
Travis Lambert, General Manager of Central Oregon Heating, Cooling, Plumbing & Electrical, oversees hiring in a technical industry where training certifications and qualifications directly affect job performance and safety.
He says, “Clear credential verification benefits everyone involved. Employers gain confidence in the qualifications behind an application, and graduates can present their credentials knowing the system behind them supports their legitimacy.”
Sector guidance can help here, especially from organizations such as AACRAO, which has published extensively on records integrity and digital transformation in registrar operations.
NIST’s digital identity guidance is useful here because it keeps attention on lifecycle management, not just initial setup.
Moving Forward
Traditional processes were built for a slower environment. They struggle against forged documents, diploma mills, altered files, and hiring timelines that do not leave much room for weeks of back-and-forth.
Secure digital credentials change that by making authenticity part of the credential itself, not something someone has to chase down afterward.
Start with a focused use case. Use standards that will still make sense later. Build privacy into the process early.
Done right, this protects legitimate graduates, gives employers faster answers, and takes avoidable strain off the people managing academic records every day.
For graduates who want to preserve and display their academic achievements properly, DiplomaFrame.com offers professional framing solutions designed specifically for diplomas and certificates.